Certified Ethical Hacker v12 Course in Delhi | CEH v12 Course ✅
May 19, 2021 2024-04-16 13:18Certified Ethical Hacker v12 Course in Delhi | CEH v12 Course ✅
Hacking Course | CEH v12 Course in Delhi | Certified Ethical Hacker Course
Bestseller
3571 Student Reviews
You may learn the Ethical Hacking in Delhi with the EC Council CEH v12 Training and Certification Course under the mentorship of primetime trainers and mentors having more than 10 years of quality experience by Craw Security – the best cyber security training institute in Delhi NCR at Saket and Laxmi Nagar branches.
- Course Duration : 40 Hours
- Language : Hindi | English
- Course Delivery : Online | offline
Book a Trial Demo Class
Training Available 24*7 Call at +91 9513805401
About the CEH v12 Training in Delhi
Learn a specialized and Certified Ethical Hacking Course in Delhi with fully intensified classroom experience via the most versatile faculties and mentors from the house of EC-council with the most advanced and latest technologically updated software of CEH v12 Training and Certification module. Become a Certified Ethical Hacker that can easily hack systems from any remote location and secure them like a genuine Security Analyst in the coolest way possible via the techniques and tactics that you will learn from our verified curriculum from ECcouncil in our authentic CEH Training in Delhi.
Learn a specialized and Certified Ethical Hacking Course in Delhi with fully intensified classroom experience via the most versatile faculties and mentors from the house of EC-council with the most advanced and latest technological updated software of CEH v12 Training and Certification module. Become a Certified Ethical Hacker that can easily hack systems from any remote location and secure them like a genuine Security Analyst in the coolest way possible via the techniques and tactics that you will learn from our verified curriculum from ECcouncil in our authentic CEH Training in Delhi.
The persons who are interested in making a shinier career in the stream of Cyber Security Course and Ethical Hacking Course in Delhi can get easily get enrolled in this suitable training of Ethical Hacking Course in Delhi after 12th for getting a massive kick-start for your professional career. Craw Cyber Security Institute is the Best Institute for Ethical Hacking in Delhi with an in-depth curriculum having the syllabus duly verified from the reputed ECcouncil and through a team of expert Cyber Security professionals.
Getting admission to a CEH v12 Course in Delhi helps you in mastering a CEH Certified Ethical Hacker methodology. The skills you will learn there can be used in penetration testing or ethical hacking v12 situation. When you will finish the course, you will come out with hacking v12 skills that are in high demand along with the internationally recognized Certified Hacker certification. This course will also prepare you for EC Council Certified Ethical Hacker Exam.
CEH v12 Course Content
Module 01: Introduction to Ethical Hacking
Module 02: Footprinting and Reconnaissance
Module 03: Scanning Networks
Module 04: Enumeration
Module 05: Vulnerability Analysis
Module 06: System Hacking
Module 07: Malware Threats
Module 08: Sniffing
Module 09: Social Engineering
Module 10: Denial-of-Service
Module 11: Session Hijacking
Module 12: Evading IDS, Firewalls & Honeypots
Module 13: Hacking Web Servers
Module 14: Hacking Web Applications
Module 15: SQL Injection
Module 16: Hacking Wireless Networks
Module 17: Hacking Mobile Platforms
Module 18: IoT Hacking
Module 19: Cloud Computing
Module 20: Cryptography
EC-Council CEH v12 Our Course Advisor
CEH v12 Course in Delhi | Ethical Hacking Course
Eccouncil accredited CEH v12 Course in Delhi and Training Institute is to help you to become a master in the Certified Ethical Hacker v12 Course in Delhi (Eccouncil CEH – Certified Ethical Hacker v12) that can be used in Penetration Testing and Ethical Hacking techniques to process some certain skillset of qualified methods of working in the domain of Cyber Security Course and Ethical Hacking.
When you walk out of Craw Cyber Security Institute with Ethical Hacking and Cyber Security skills that are highly in demand and carry the same value as an internationally certified Ethical Hacker Course, you get the most out of it. In conclusion, this Ethical Hacking Course in Delhi prepares you for the Eccouncil CEH – Certified Ethical Hacker certification v12 exam.
What will you Learn in CEH v12 Course in Delhi | Ethical Hacking Course
Ec-council CEH v12 Course in Delhi and Training Institute is to help you to become a master in the Ethical Hacking Course in Delhi (Ec-council CEH – Certified Ethical Hacker v12) that can be used in Penetration Testing course, an Ethical Hacking Course in Delhi, India. When you walk out of an Ethical Hacking Institute with Ethical Hacking and Cyber Security skills that are highly in demand and carry the same value as an internationally certified Ethical Hacker Course, you get the most out of it. In conclusion, this Ethical Hacking and Cyber Security Course in Delhi will prepare you for the Ec-council CEH – Certified Ethical Hacker certification v12 exam.
Choose Your Preferred Learning Mode

Classroom Training
We offer customized VILT (Virtual Instructor-Led Training) sessions at your convenient hours to provide effortless training.

Online Training Class
One can also opt for the prerecorded video sessions available at any point of time from any particular location.

Corporate Training
Hire a preferred trainer at your work premises at your chosen time slots and train your employees with full efficiency.
CEH v12 Course Description
The magnificent training of the Certified Ethical Hacking Course in Delhi NCR via Craw Cyber Security Institute in Saket and Laxmi Nagar locations in Delhi is the collection of thoughts and industrial insights of highly qualified professionals with years of experience and expertise in hand. This CEH v12 Training & Certification has been offered from a vast curriculum duly recognized by the esteemed EC Council and offered by some of the industry-oriented expert faculty members and mentors possessing many years of experience in providing quality training to the students in so many reputed institutions in India.
Enroll in a Cyber Security Course | Certified Ethical Hacking Course with us and become specialized in hacking computer systems and securing them like the experts. We provide the best EC-Council Certified Ethical Hacker CEH v12 Training and Certification in Delhi. The CEH Certified Ethical Hacker v12 (CEH v12 Course in Delhi) program is a top-rated information security training program among information security professionals. Enrolling in a CEH v12 Course in Delhi helps cover all concepts in the objectives so that you can master the knowledge needed to clear the CEH Exam.
The latest version of EC Council Certified Ethical Hacker v12 has just launched on Wednesday, 7th September 2022 with a worldwide release through the EC Council platform. However, there are several specializations and updates announced with the same release of CEH v12 with no change in the number of modules. Some of the prominent changes in technology are as follows:
EC Council C|EH v12 Content Updates
New Learning Framework:
Learn
Certify
Engage
Compete: New challenges every month!
100% compliance with the NICE 2.0 Framework
Based on a comprehensive industry-wide job task analysis
Hands-on Learning Labs
Practice Range
Global C|EH community competitions
Cheat sheet
Coverage of the latest malware
Lab-intensive program (every learning objective is demonstrated using labs)
Hands-on program (50% of training time is dedicated to labs)
Lab environments that simulate real-time environments
Covers the latest hacking tools (based on Windows, macOS, and Linux)
Latest OS covered and a patched testing environment
Updated versions of tool screenshots, tool listing slides, and countermeasure slides
Learn about the new challenges that are coming every month for the new-level ethical hacking practitioners in the following table:
| Month | Skill Challenge |
| October 2023 | OWASP Top 10 Web Application Threat Vectors |
| November 2023 | Ransomware/Malware Analysis |
| December 2023 | Outdated/Unpatched Software |
| January 2024 | System Hacking and Privilege Escalation |
| February 2024 | Web Application Hacking and Pen Testing |
| March 2024 | Cloud Attack/Hacking |
| April 2024 | Social Engineering/Phishing attacks |
| May 2024 | IoT Attack/Hacking |
| June 2024 | Wi-Fi Network Attack/Hacking |
| July 2024 | DOS/DDoS Attack |
| August 2024 | Mobile Attack/Hacking |
| September 2024 | Supply Chain Cyber Attacks |
If you are looking for a good and professional Ethical Hacking Course in Delhi, then Craw Cyber Security Institute in Saket and Laxmi Nagar locations in Delhi could be the perfect spot for you to learn the crucial Eccouncil CEH v12Course in Delhi as it falls under the category of Top 10 Ethical Hacking Institute in Delhi. While learning here, you will get proper Training & Certifications in Ethical Hacking Courses so that you can also use techniques and tactics duly utilized in the industry by the Best Ethical Hackers and Penetration Testing Experts from this field.
Moreover, the Certified Ethical Hacker v12 course in Delhi starts with a general overview of security essentials. After that, you will start learning system, network, and web services security before diving deep into wireless and Internet security. The main benefits of taking a CEH v12 Course in Delhi are:
It provides the breadth of coverage necessary to learn the full security concepts behind the CEH exam.
It assists in preparing you for a career as a Cyber security professional.
If you want to make a career in Cyber Security, then getting admission for the ethical hacking V12 training and certification program is quite essential. CEH v 12 Course in Delhi is a leading training and certification program where Students audit a system for weaknesses and vulnerabilities using the same tools and exploits as malicious hackers but having proper legal rights and working towards the cyber security of an organization. One of the most important things about being a proficient hacker is that you understand the psyche of how a hacker’s brain works.
By taking the CEH v12 Course in Delhi, you will be in a better state to be at the helm of an organization’s cyber security. In today’s day and age, when cyber security is a top priority in every organization, taking up a Certified Ethical Hacker v12 Course will give you an edge over others in this field. The Certified Ethical Hacker (CEH v12) program is the most coveted information security training program any information security professional wants to learn. Completing this course will help you in acquiring hacking technologies within the legal framework of the country, which you can use in ethical ways.
Training in this course gives you proper knowledge of advanced hacking tools and techniques used by hackers and information security professionals across the globe.
Workshops & Seminars: We Provide Workshops and Seminars to Fill the Gap Between Industry requirements and Students’ Skills.
100% Job Guaranteed: At Starting Package 4-5 Lacs per annum After EC-Council Training from Craw Cyber Security Institute.
At Craw Security, you will encounter India’s best-paid cybersecurity training offered under the primetime mentorship program proposed by highly decorated and skilled instructors with many years of esteemed experience in delivering quality training. In addition, the paid cybersecurity training will provide the advanced fundamentals associated with the cybersecurity industry that can be very crucial to enhance the mental level of learners with respect to proposing the top-notch CEH v12 Training and Certification in Delhi.
There can be many paid online cyber security courses for beginners that can be proven game-changing aspects for a learner’s career in shaping the skills of cyber security to an optimum level. In this regard, this course is genuinely curtailed for the current tech professionals in the industry that are nicely equipped with some decent designations in any organization across the globe and have a shortage of time to come for taking the course with physical presence at the premises of Craw Security.
Moreover, the learners will also obtain India’s top-notch instructors in offering them the best cyber security paid online certification courses under the same category trainers that propose the offline version of cyber security training.
Craw Security's Students Awarded










EC Council C|EH v12 Technology Updates
● MITRE ATT&CK framework
● The diamond model of intrusion analysis
● Techniques for establishing persistence
● Evading NAC and endpoint security
● Fog computing
● Edge computing
● Grid computing
Related Cyber Security Course
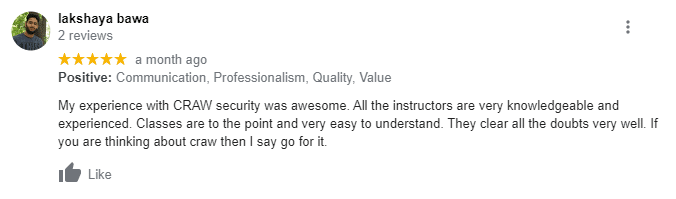
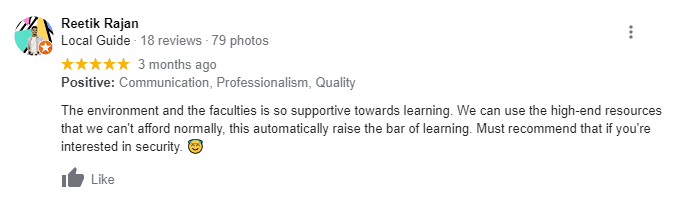
What People Are Saying About Craw Security
Google Review (1,616) ★★★★★

EC-Council CEH v12 Frequently Asked Questions
This is a very problematic question for varied Certified Ethical Hacker v12 aspirants, but the answer is yes. It is a harder exam in comparison to Arts and Humanities exams but a bit easier than the streams related to medical and engineering.
Many institutes in the open are providing crucial training in CEH v12 Certified Ethical Hacker Course, but the Best Institute for Ethical Hacking in Delhi is Craw Cyber Security Institution, located in two premium spots such as Saket and Laxmi Nagar in New Delhi, India.
Yes, it’s very certain that pursuing the Certified Ethical Hacking Course in Delhi is a good and shinier career ahead in case you have a keen interest in Ethical Hacking and a Cyber Security background. One can nicely join our Certified Ethical Hacking Training and Certifications from Craw Cyber Security Institute in Saket and Laxmi Nagar locations and learn from scratch to become a genuine Cyber Security professional in the shortest possible time.
- Computer Networking Skills.
- Computer Skills
- Linux Skills
- Basic Hardware knowledge
- Cryptography Skills
- Database Skills
List of Companies you can get placements in
Company Name | Contact Person | E- Mail | Contact Number | Course Name |
|---|---|---|---|---|
Deep Logictech India Pvt Ltd | Nidhi | hr4@deeplogictech.com | +011-45453628 | Ethical Hacker |
British Telecom | Binit Rai | binit.rai@bt.com | +91-7595920106 | Cyber Security Professional |
Fastandfurious Consulting | Niharika Sharma | hr2@fastandfuriousconsulting.com | +91-9990291119 | Networking |
Parahit Technologies Ltd. | Pooja Thakur | ptlhr@parahittech.com | +91-9149292929 | Technical Support Engineer(CCNA) |
Trigent Software Limited | Hafsaa Sait | hafsaa_m@trigent.com | +91-9886970024 | L1 Technical Support Engineer |
Shriv ComMedia Solutions Pvt. Ltd. | Aarti Singh | aarti@commediait.com | +91-9910967277 | Software Developer |
HCL Technology | Anamika | hr@evisions.co.in | +91 9811722023 | Network Administration, Security |
BreachLock | BreachLock | hello@breachlock.com | +1 917-779-0009 | Penetration Tester with Python Development |
Right Step Consulting | Right Step Consulting | resume@rightstepconsulting.com | +0120-429 1013 | Network Administrator |
ACE IT Solutions | ACE IT Solutions | Info@aceits.net | +646-558-5575 | Junior Cyber Security Analyst |
Limpidstone Technology Pvt. Ltd | Manisha Saini | info@limpidstone.com | +91 7840060051 | CEH |
Indian Institute of Management and Development | IMMD Placement | info@iimdindia.com | +020 - 6500 1155 | L 1 Engineer |
Indian Institute of Management and Development | IMMD Placement | career@vsure.in | +91 9354061269 | Network Administrator |
Indian Institute of Management and Development | IMMD Placement | career@vsure.in | +91 9354061269 | L 2 Engineer |
Indian Institute of Management and Development | IMMD Placement | career@vsure.in | +91 9354061269 | Accounts Executive |
Three D Integrated Solutions Ltd | Uma Verma | uma.verma@threeds.com | +91 874507070 | Certified Ethical Hacker (CEH v12) |
IARM Information Security Pvt Ltd | Sridhar | sridhar@iarminfo.com | +91 9361906659 | C|EH v12 |
IARM Information Security Pvt Ltd | Sridhar | sridhar@iarminfo.com | +91 9361906659 | SOC Analyst |
LINC Education Services | Avani Raghuvansi | avani@linceducation.com | +91 7045577921 | Cyber Security |
Mekdam Technical Services | Abdul Saiyad Khan | a.syed@mekdamholding.com | +91 9908403117 | Scada Security |
Precise Testing Solution Pvt Ltd | Sonali Sharma | hr@precisetestingsolution.com | 0120 - 45555590 | EC-Council |
RDX | Navisite Pvt Ltd | Naveen Kumar | nkumar@rdx.com | +91 7411602488 | Sr. Consultant |
Aujas Technology Pvt Ltd | Pankaj Badera | pankaj.badera@aujas.com | +91 7696506250 | Sr. Consultant |
Tetra Information Services Pvt. Ltd. | Mitali | mitali@tetrain.com | +91 7024125214 | Linux |
Orbit India | Pragati Choudhary | hr.orbit@orbitindia.net | 011 - 49141500 | CCNA |
Percoyo Pvt Ltd | Dorai Raj | hr@percoyo.com | +91 8660333455 | Stack Developer |
AAITPro | Kartik Beemsingh | kartib@aaitpro.com | +91 9789905286 | CCNA |
Experis | Nidhi | nidhi.sharma@in.experis.com | +91 9810182383 | SAP |
Seek Your Job | Kumara | cv@seekyourjob.com | +91 9443455374 | Web Development |
Art Kart | Anil Pakhare | art.kart00@gmail.com | +91 9082452620 | Android |
Ideas2it | Dhanasekar | dhanasekar@ideas2it.com | +91 8681059189 | Software Testing |










