Best Penetration Testing Course in Delhi, India
June 11, 2021 2025-06-11 18:20Best Penetration Testing Course in Delhi, India
Learn Advanced Penetration Testing Course Training with AI in Delhi
Bestseller
2000+ Student Reviews
The invaluable Penetration Testing Course is a training and certification course that delivers the required information for extracting vulnerabilities, threats, and loopholes in varied IT infrastructures of a target organization. For example, Craw Security has all the necessary training staff and the relevant classroom as well as lab facilities to impart quality pentesting training among students.
- Course Duration : 60 Hours
- Language : Hindi | English
- Course Delivery : Online | offline
FutureSkills Prime Partner (A MeitY NASSCOM Digital Skilling Initiative)
Accredited by NASSCOM, approved by the Government of India
Book a Trial Demo Class
Training Available 24*7 Call at 9513805401
Best Penetration Testing Full Course
Learning the high-end course of Advanced Penetration Testing with AI in the vicinity of Delhi NCR at the superb educational branches in Saket and Laxmi Nagar locations by Craw Cyber Security Institute has been remarkably present in the global market for more than a decade. Under the observation of primetime penetration testers, Craw Security furnishes the best-in-class Penetration Testing Course for Beginners with AI with all the fundamental knowledge being imparted by industry professionals thoroughly trained for imparting quality training. In the Advanced Penetration Testing Course Training with AI in Delhi, one will certainly have a comprehensive introduction to pentesting with AI features.
In addition to this, all the learners who wish to hone their current skills in penetration testing get more sharpened can nicely join this Advanced Penetration Testing Course Training in Delhi by Craw Security’s superb training instructors with many years of quality experience. Along with that, learners will also get a chance to get duly trained and counseled by Mr. Mohit Yadav, a renowned cybersecurity expert all over the globe.
Book a Trial Demo Class
Training Available 24*7 Call at +91 9513805401
What will you learn in the Advanced Penetration Testing Course with AI?
A person with a deep interest in learning the varied fundamental concepts associated with the Advanced Penetration Testing Course with AI can sincerely opt for this enhanced Penetration Testing Course for Beginners through a highly verified curriculum acclaimed by numerous cyber security experts all over the globe. In addition, a sincere learner will also have the benefit of getting the top-notch AI-based penetration testing certification that will be particularly valid in almost every major and minor IT organization in the worldwide market.
Moreover, after going through this Advanced Penetration Testing Course with AI under the influence of a superb trainer as well as mentor, one would also become a certified professional who can find potential vulnerabilities, threats, and loopholes in the varied IT infrastructures and secure an expert security analyst.
In this regard, students who wish to go to a certain level and learn this proactive approach of studying this primetime Advanced Penetration Testing Course in Delhi NCR by highly qualified training professionals with 10+ years of quality experience can seek admission in this genuine training program at the earliest.
Best Penetration Testing Full Course
This particular AI-based Penetration Testing Course for Beginners is the finest course that you can get in the Best Penetration Testing Full Course with AI in the vicinity of Delhi NCR at the two most prominent locations. Further, one will get proper exposure to every nitty-gritty detail concerning the best-in-class Penetration Testing Course for Beginners in order to enhance one’s knowledge quotient and have a proper introduction to pentesting with AI fundamentals.
Moreover, after understanding the prime concerns of our learners related to time management, we have also introduced a very genuine and the best penetration testing course online with AI under the guidance of the same category of trainers that are offering the offline version of the course. Furthermore, this prominent penetration testing course with AI is nicely accredited by FutureSkills Prime, a MeitY – NASSCOM digital skilling initiative that is duly accredited by the government of India.
Penetration Testing Course Content
Lesson 01: What is Advanced Penetration Testing (APT)
Lesson 02: Types of Penetration Testing & Areas
Lesson 03: Demo Report Understanding
Lesson 01 : Scan All Top 20 Ports
Lesson 01: Basics of Exploitations
Lesson 01: Basic of Linux Commands
Lesson 02: Permission Commands
Lesson 01: Introduction to Kali Linux
Lesson 01: Introduction to Bash Scripting
Lesson 02: Bash Scripting Fundamentals
Lesson 03: Tool Creation – Password Generator
Lesson 04: Functions
Lesson 01: Essential Tools
Lesson 01: DNS Enumerations
Lesson 02: Automating Lookups
Lesson 03: DNS Zone Transfers
Lesson 04: NMAP and Masscan
Lesson 05: Port Enumeration
Lesson 01: Website Recon
Lesson 02: Netcraft, Shodan, Email Harvesting
Lesson 03: OSINT Framework
Lesson 01: Introduction of BOF
Lesson 02: Basic Data Structure Understanding
Lesson 03: Types of BOF
Lesson 01: CTF on BOF
Lesson 01: CTF on Fixing Exploits
Lesson 01: Find Exploits on Google Hacking Database
Lesson 02: Find Exploits on GitHub
Lesson 01: Introduction to Antivirus Evasion
Lesson 02: Working of Antivirus Evasion
Lesson 03: Obfuscation Techniques
Lesson 01: File Transfers Using FTP, Telnet, SSH, PHP, Python
Lesson 01: Service Exploits – Insecure Service Permissions
Lesson 02: Service Exploits – Unquoted Service Path
Lesson 03: Service Exploits – Weak Registry Permissions
Lesson 04: Service Exploits – Insecure Service Executables
Lesson 05: Registry – Auto Runs, etc.
Lesson 01: Service Exploits
Lesson 02: Weak File Permissions – Readable /etc/shadow
Lesson 03: Weak File Permissions – Writable /etc/shadow
Lesson 04: Weak File Permissions – Writable /etc/passwd
Lesson 05: Sudo – Shell Escape Sequences, etc.
Lesson 01: Password Spraying and Dictionary Attack
Lesson 01: Port Redirection and Tunneling Using Chisel
Lesson 01: Introduction of AD
Lesson 02: Basics of AD
Lesson 03: Enumeration of AD
Lesson 01: Introduction of Empire
Lesson 02: Getting Shell Using Empire
Lesson 01: Introduction to Penetration Testing Labs
Lesson 02: Hands-On Practice
Lesson 01: Understanding Penetration Test Reports
Lesson 02: Debriefing and Recommendations
Lesson 01: Proof of Concept (POC)
Lesson 02: Executive and Management Report
Lesson 03: Technical Report For IT and security Department
Talk to Our Course Advisor
Why Choose Craw Security for the Advanced Penetration Testing Course with AI in Delhi?
Several reasons are there that give world-class support to our viewpoint of Craw Security being the Best Penetration Testing Training Institute in India with full AI features and characteristics in the course curriculum and well-qualified training professionals with 10+ years of experience. Some of the main factors related to this are mentioned below:
- Well-trained and duly qualified training professionals with more than 10 years of classic work experience.
- Duly verified study materials from cybersecurity experts cum penetration testers working on various highly decorated designations worldwide.
- This training will be oriented around actual projects, and it will be required of all candidates.
- Unlimited flexibility to choose the styles of instruction for the course, including but not limited to:
- VILT (Virtual Instructor-Led Training) Sessions,
- Pre-Recorded Video Training Sessions, and
- Classic Classroom Training Sessions.
- Complete access to both digital and hard copies of the study materials just for the purpose of enhancing the process of knowledge collection.
- Availability of recordings for training sessions (limited to VILT training mode).
Key Features of the Advanced Penetration Testing Course
- Introduction to Penetration Testing And Methodologies
- Penetration Testing Scoping
- Engagement Methodology
- IoT Penetration Testing Methodology
- Exploit these vulnerabilities to hack into web servers.
- Become a bug bounty hunter & discover bugs for bounties!
- Bypass security & advanced exploitation of these vulnerabilities.
Choose Your Preferred Learning Mode

Classroom Training
We offer customized VILT (Virtual Instructor-Led Training) sessions at your convenient hours to provide effortless training.

Online Training Class

Corporate Training
Hire a preferred trainer at your work premises at your chosen time slots and train your employees with full efficiency.
Craw Security's Students Awarded










Related Cyber Security Course
Latest Blogs
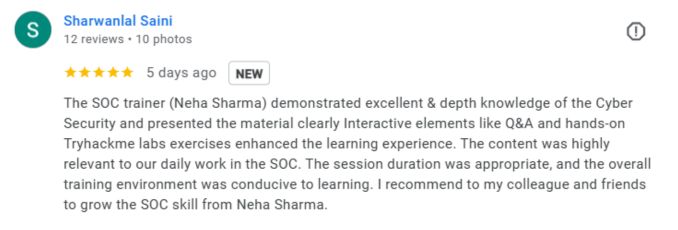
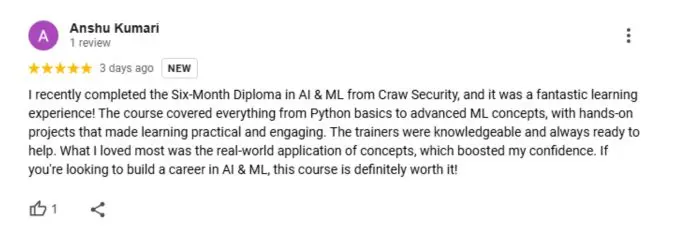
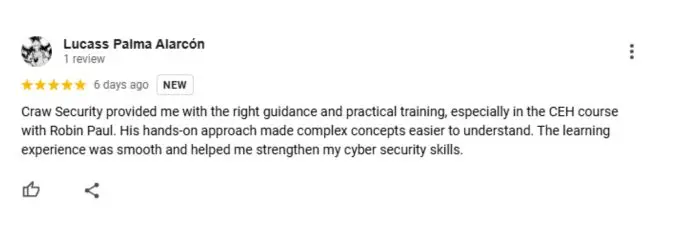
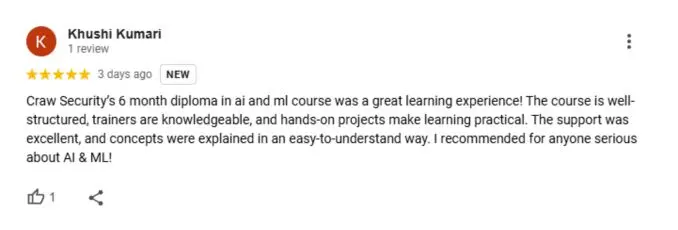
What People Are Saying About Craw Security
Google Review (2000+) ★★★★★
Companies you can get placements in

Frequently Asked Questions
The invaluable Penetration Testing Course is a training and certification course that delivers the required information for extracting vulnerabilities, threats, and loopholes in varied IT infrastructures of a target organization. For example, Craw Security has all the necessary training staff and the relevant classroom as well as lab facilities to impart quality pentesting training among students.
The most authentic Penetration Testing Course for Beginners by the super faculty members of Craw Cyber Security Institute is the best you can get to learn Advanced Penetration Testing training in the vicinity of Delhi.
You may learn the distinguished fundamentals of the Penetration Testing Course with AI in Delhi from Craw Security’s experienced trainers and mentors having more than 10 years of industry experience. You will be able to take the offline batches at the Saket and Laxmi Nagar branches of Craw Security. At the available upcoming batches, you may enquire at +91-9513805401 through our highly knowledgeable educational counsellors.
If a person is willing to start a decent penetration testing course from the very grass-root level, you may initiate it by possessing the following qualifications:
- Good knowledge of Networking fundamentals.
- Hands-on practice on varied operating systems such as Linux, Windows, etc.
- Good knowledge of coding skills or programming languages like Python, C, C++, Java, PHP, etc.
Since it possesses long chains of coding commands to extract distinguished vulnerabilities, threats, and loopholes in numerous IT infrastructures of a target organization, it is indeed a tough course to learn. However, by doing a continuous practice of the fundamental factors you may learn in the Penetration Testing Course with AI in Delhi from Craw Security, you will surely learn this course in a pretty easy manner.
You can grab the introduction to penetesting fundamentals concepts within the upcoming batches of AI-based Penetration Testing Course for Beginners at Craw Security’s Saket and Laxmi Nagar educational branches imparting quality cyber security training.
Yes, a person who wishes to join the AI-based Penetration Testing Course in Delhi by Craw Security should possess the following factors to seek admission in the same course:
- Networking knowledge,
- Python and other programming languages,
- Good knowledge of operating systems, like Linux, Ubuntu, Kali Linux, Windows, etc.
- A solid grasp of ethical hacking concepts, etc.
The AI-based Penetration Testing Course in Delhi by Craw Security is a 60-hour long training course.
Yes, you will surely get a certificate from FutureSkills Prime, a MeitY – NASSCOM, Digital Skilling Initiative, after successfully completing the examination from the FSP.
Yes, there is a practical lab component in this AI-based Penetration Testing Course in Delhi by Craw Security. Learners can grab the same during our course training through our highly efficient and skilled educators with years of quality experience in the same trajectory. To know more about the same, give us a call at +91-9513805401 and have a word with our team of educational counselors.
The course is nicely structured with both theoretical and practical concepts so that every learner can understand things nicely and grasp all the concepts genuinely.
Yes, you need to bring a laptop with a specialized set of features to your classes at Craw Security to understand things properly and work efficiently on your concepts without any hurdles.
- Ethical Hacking: The term “ethical hacking” refers to a comprehensive notion that involves the deliberate application of hacker-like tactics authorized by the owner of a system to uncover weaknesses inside that system. Ethical hacking possesses an exploratory characteristic, wherein the ethical hacker uses several approaches and tactics to systematically identify and exploit a multitude of vulnerabilities.
- Penetration Testing: The proposed technique exhibits a higher degree of focus and structure. Penetration tests often possess a defined scope and aim, encompassing endeavors such as attempting to gain unauthorized access to a certain dataset or showcasing the exploitation of a known vulnerability.
As per Ambition Box, there is a wide range of salaries available for penetration testers in India, ranging from ₹ 2.4 Lakhs to ₹ 19.0 Lakhs, with an average yearly pay of ₹ 8.9 Lakhs. The estimations of salaries are derived from the most recent earnings that were received from 597 penetration testers with seven years of experience.
Yes, penetration testing with AI can indeed be a hard profession since it needs you to anticipate the behaviors of a hacker and uncover weaknesses in a company’s security system that others may have overlooked. Penetration testing also necessitates the possession of advanced computer abilities, which can be acquired through a significant amount of time and effort.