Best Online End Point Security Course in Delhi | End Point Security Training
Bestseller
3571 Reviews
472,125 students
Download Craw Academy Application
- Course Duration : 40 Hours
- Course Level : Intermediate
- Course Delivery : Online Videos
- Language : Hindi, English
- Accreditation by : Craw Cyber Security
₹2,999.00₹15,000.00
Book a Trial Demo Class
Training Available 24*7 Call at +91 9513805401


What will you Learn in End Point Security Course in Delhi
The Online End Point Security Course duly provided by Craw Cyber Security Institution is one of the Best 7 Best Endpoint Security Courses in Delhi that are worthwhile of doing but we have the Best Endpoint Security for Analysts Training since we are fully accredited from various recognizing bodies that are giants in the Cyber Security domain for many years such as EC-Council, Red Hat, CompTIA, CISCO, and many more.
Craw Cyber Security offers the best Endpoint Security Fundamentals Course that tracks and hunts even the next-generation viruses and programming malware in your endpoint devices from a centralized system with a single go. It comes with an in-built system with seamless protection that doesn’t come in your typical antiviruses and firewalls by utilizing machine learning and fuzzy logic to detect that that bypasses your traditional protection mechanism. The endpoint is one of the most critical parts of the network to defend, particularly since network threats often affect the weakest link in a network’s security. You will get the Best Endpoint Security Certification by signing up for this course through our online courses portal.
Endpoint Security Course Content
Course Curriculum
Module 01 : Implementing Internet Security Anti Virus
Module 02 : Two-Factor Authentication Implementation
Module 03 : Mobile Device Management For Industry
Module 04 : Data Loss Prevention Overview & Implementation
Module 05 : Security Information and Event Management (SIEM)
Module 06 : APT- Attack
Module 07 : MITRE Framework
Module 08 : EDR
Module 09 : MDR
Module 10 : Next Generation Firewall
Module 11 : Unified Threat Management
Module 12 : Physical Security
Module 13 : ISO 27001 Lead Auditor Guidelines
Endpoint Security Our Course Advisor
[popup_anything id=”116469″]
Endpoint Security Course in Delhi
The curriculum of our Online Endpoint Security Course in Delhi also comprises the fundamental training on Endpoint Detection and Response (EDR), which is widely known as Endpoint Detection and Threat Response (EDTR) that is an endpoint security solution that regularly controls the final consumer devices to track, detect, and respond to cyber vulnerabilities such as ransomware and malicious actors.
Endpoint security is the way toward getting the different endpoints security on an organization, regularly characterized as end-client gadgets like cell phones, workstations, and work area PCs, in spite of the fact that equipment, for example, workers in a server farm are additionally viewed as endpoints security. Exact definitions fluctuate among thought pioneers in the security space, however basically, endpoint security tends to the dangers introduced by gadgets associating with a venture organization.
Requirements
- Elementary IT Skill.
- An interest in learning about Security.
- Computer with a minimum of 8GB Ram.
- Dedication towards learning the course.
- Knowledge of the internet required.
Choose Your Preferred Learning Mode

Classroom Training
We offer customized VILT (Virtual Instructor-Led Training) sessions at your convenient hours to provide effortless training.

Online Training Class

Corporate Training
Hire a preferred trainer at your work premises at your chosen time slots and train your employees with full efficiency.
Endpoint Security Course Description
The future is now revolving around smart gadgets and internet-enabled electronic devices that use Artificial Intelligence to complete your most of the functions in a single open-source internet connection. Hence, the malicious actors or entities can gain access to your smart device doing multiple functions for your and can compromise them at their own free will and to secure these smart devices from being bullied by those cyberattacks one needs to secure them using Endpoint Security protocols that vanishes the ill-practices from being entering into your devices servers by securing all entry and exit points.
The benefits of endpoint security include:
Protection for devices – Including, besides traditional malware like ransomware and Trojans, file-based and file-less script attacks and malicious JavaScript, VBScript, PowerShell, and other macros. Cost savings – By obstructing the necessary remediation of malware-ridden devices, protecting trade secrets and other intellectual property, aiding device performance, and preventing ransomware attacks. Time savings – By freeing up IT staff or managed service providers to focus on main business objectives, ensuring uptime for all devices, and streamlining the management and prevention of online threats. Compliance satisfaction – Many organizations are governed by data security regulations which are required special precautions against the theft of private personal data, like retail, healthcare, and the public sector to name just a few.
It may be any device such as smartphones, tablets, desktops, laptops, even your smartwatch is connected to the internet via linking through your phone’s Bluetooth – everything is connected to a single source of internet server hence, all Internet of Things or IoT are connected to one another utilizing a single open-source connection and can be hacked using a single thread command for a unified network. Therefore, the need of securing your integrated network connection is majorly important than anything else as they provide an entry point for threats.
Online Endpoint Security Course in Delhi will assist you to secure every single possible endpoint or entry point linked together to a single open-source network by blocking the ill-access attempts and other varied risky behaviors at these so-called Entry or Exit points. As more organizations adopt practices such as BYOD (Bring Your Own Device) and remote/mobile employees, the enterprise network security perimeter has basically dissolved. Now, it’s your own responsibility to secure your IoT devices as soon as possible by learning this excellent knowledge possessing Online Endpoint Security Course.
Craw Security's Students Awarded










Course Highlights
- Implementing Internet Security Anti Virus.
- Mobile Device Management For Industry
- Security Information and Event Management
- Two-Factor Authentication Implementation
- Data Loss Prevention Overview & Implementation
- Unified Threat Management
- Next-Generation Firewall
- ISO 27001 Lead Auditor Guidelines
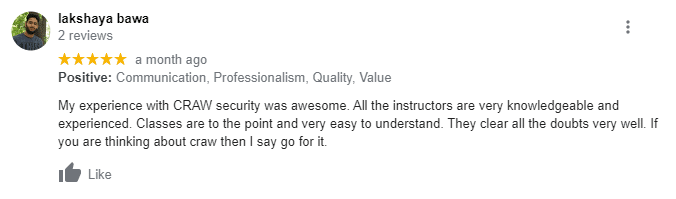
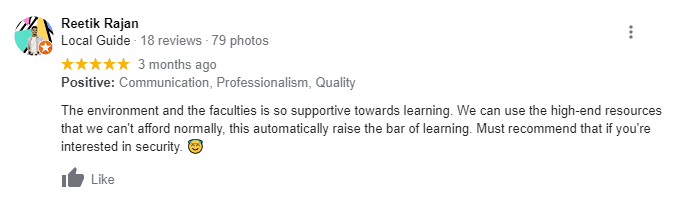
What People Are Saying About Craw Security
Google Review (1,586) ★★★★★

Endpoint Security Frequently Asked Questions
The world now needs the security of their smart devices that can be exploited by using some ill-practice of Black Hat Hacking. We have maintained a list that requires Endpoint Security at the most crucial level such as:
- Internet of Things (IoT) Security.
- Antivirus Solutions.
- Endpoint Detection and Response.
- URL Filtering.
- Application Control.
- Network Access Control.
- Browser Isolation.
- Cloud Perimeter Security.
- Endpoint Encryption
- Secure Email Gateways
- Sandboxing
The main key features that contain the prime functional Endpoint Security Products are such as:
- Application whitelisting or control.
- Network access control.
- Data classification
- Data loss prevention.
- Endpoint detection and response.
- Insider threat protection.
- Disk, endpoint, and email encryption
Privileged user control.
Adopting Endpoint Security Solutions comprise your whole network protection against varied sorts of cyberattacks while antivirus software will only track down the malicious entities coming from a single or unique endpoint.
There are 5 major elements of a Successful Strategy to conveniently securing an Endpoint:
- Precisely do the fundamentals.
- Understand the Endpoints.
- Assign Advanced and Automated Endpoint
- Prioritize and Automate Detection and Response.
- Make Employees Your Ally.
The Craw Cyber Security Certification was duly delivered to various students doing several certifications and diploma courses in the Cyber Security domain. It is delivered by Craw Cyber Security Institution for both online as well as offline courses for IT Security entry-level courses for beginners, certainly a nice reference point to start your IT journey.
Endpoint Security Solutions can be referred to as the exercise to secure your smart electronic devices such desktops, laptops, tablets, smartphones, and other smart devices from being cyberattacked by some malicious entities and campaigns. It is done by some Endpoint Security Software that allows enterprises to secure their IoT devices that are used in a bulk manner in their organization in a hefty amount on cloud or network interfaces.
Endpoints in Clouds or widely termed as Cloud Endpoints is basically is an API Management System that protects, controls, analyses, and organizes quotas on your APIs. Endpoints use the Extensible Service Proxy (ESP) or Extensible Service Proxy V2 Beta (ESPv2 Beta) to host your APIs.





