PESTUDIO Major Tool for static analysis
PESTUDIO Major Tool for static analysis
What is PESTUDIO, and how can it be used? To know that this article will help you the most. In this article, you’ll learn how to fully access this tool to do a static analysis. Let’s continue to the steps forward.
PESTUDIO
Pestudio allows professionals to analyze any PE file without execution. When in use, it will examine all sections that contain important data about PE structure. However, we only need to have a look at some important values in the section, and each section speaks a lot.
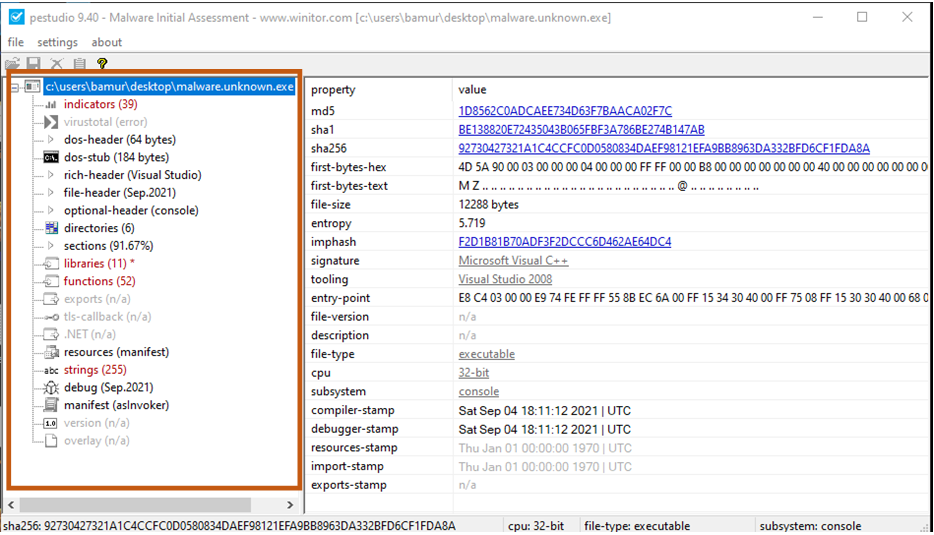
Indicators
They store all functions that seems suspicious. Remember, those indicators will show different kinds of information that you need to note down logically. That’s to do for doing perfect analysis. In the process of examining sample, you’ll have to think where it’ll wrong if any dysfunction happen which is not proper according to the practitioner.
You should at the screenshot.
According to the screenshot, you can see that there is a URL pattern. Also, if you look at it correctly, you’ll see that it won’t feel good to look at it. That’s because we are examining a sample, which probably could be a malware, and possibility is that it could be not.
Then you can take it as a suspicious activity. After that, you need to note down this, and also the path that you saw. Also, you can use .dll that is used by this sample.
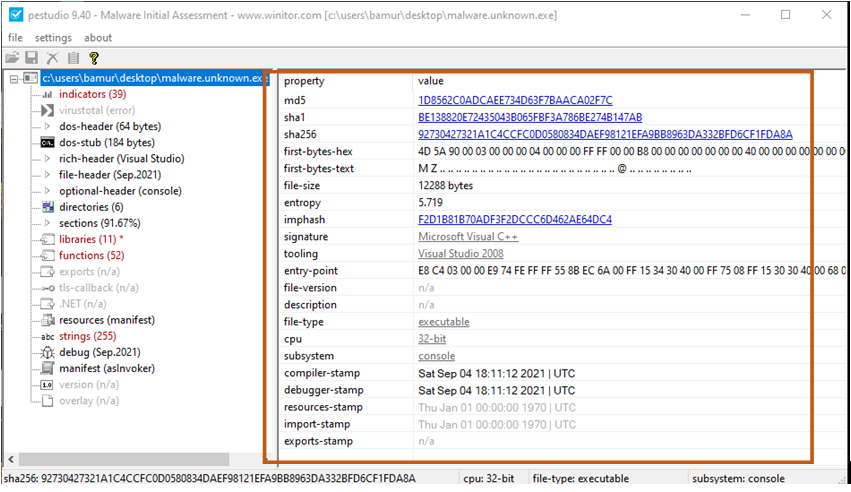
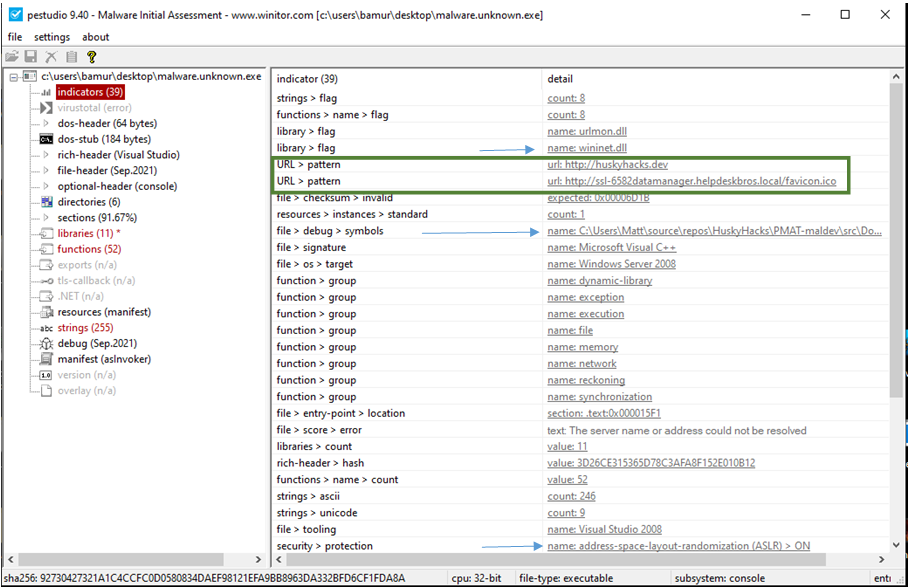
If we look at the information on the right side, we can see that several things are defined over there. Look in the screenshot for perfect calculation. You probably will be seeing MD5 and SHA1 SHA256. These two elements are the hash for this file. Also, we can say that these are fingerprints, and it’s unique own on its own.
Hash is helpful in scanning virus total, so that we can examine its hash and get more data. Rather than that this file will act malicious or not. However, still, we can’t jump to any conclusions that the file is a virus or malware. There is so much to do to prove it’s malicious or not. Make sure you don’t leave any notes unwritten that locally doesn’t fit as logical.
Further, the crucial thing that must be noted down is its first-byte text, aka magic value symbolled as MZ. Also, the File Size only indicates the file size in bytes. It’ll be shown in MB.
Second to that indication is to see if it shows packed or not ENTROPY show. Moreover, if it shows any disorders inside the sample. If you observer this value above 6.9, then you can say it seems to be packed.
Next thing to do is to point out its signature and tooling. You might be able to see that it contains a signature type C++, where the tool is visual studio. Moreover, we have file type and CPU arc. We’ll be able to confirm that this is operable, where the CPU is 32-bit. Mix and debug stamp here. Now, you should note down that when it was created and when it was debugged.
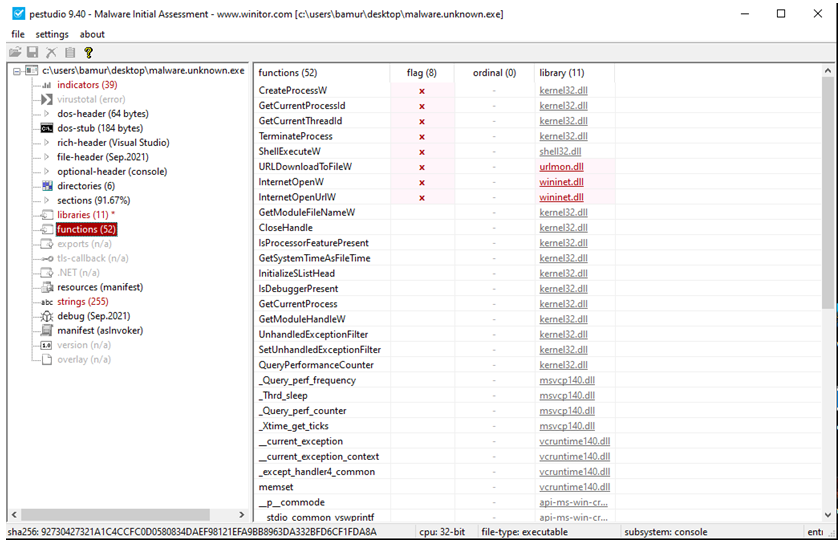
Let’s go right to the function section. It contains all functions that .dll provided to execute this sample. That’s why you can see the red cross in the screenshot. It proves that those functions are suspicious and can be possibly a potential harmful feature in your system. Therefore, you’d need to logically connect with indicators.
The most crucial thing in PESTUDIO is to analyze STRINGS that says a lot about the sample, as you can obviously see in the screenshot.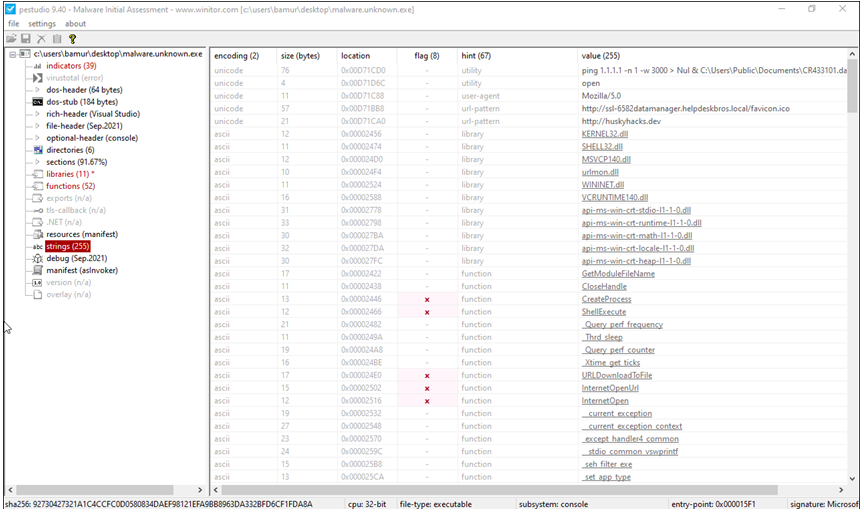
Now, the step is to read the strings which will tell you many things about the sample, and how you can analyze its IOCs. As we have already mentioned, PESTUDIO is crucial when it comes to Static Analysis. Several tools will help you to identify IOCs such as – PEVIE, PEID, CFF EXP. if you want to learn about this tool in depth, and other tools, you can join our classes. SO will see another tool in the next session, so keep connected.
Learn More!
As we know that cyber security cases have increased in the few years, we need to update ourselves with it too. To get latest cyber security related news! Learn, Research, and Grow!












