Basic Networking Course in Delhi
June 11, 2021 2025-06-04 13:39Basic Networking Course in Delhi
Basic Networking Course with AI in Delhi | Networking Course with Certification
Bestseller
2000+ Student Reviews
Learn The Fundamentals of Networking Course with AI with the most experienced trainers and mentors group in town to understand all the basic concepts associated with the Basic Networking Course with AI for Beginners. In addition, our world-class teaching faculties provide in-house, hands-on practice on the latest devices, labs, server racks, etc.
Moreover, Craw Security also offers its dedicated labs access to its prime student group at a round-the-clock facility. This in-depth Basic Networking Course in Delhi offers students the best knowledge and skills to pursue a greater career in the field of Networking without engaging in any extra training.
- Course Duration : 60 Hours
- Language : Hindi | English
- Course Delivery : Online | offline
FutureSkills Prime Partner (A MeitY NASSCOM Digital Skilling Initiative)
Accredited by NASSCOM, approved by the Government of India
Book a Trial Demo Class
Training Available 24*7 Call at 9513805401
What will you learn in the Basic Networking Course with AI in Delhi?
Anyone who wants to learn networking basics can dedicate themselves to the magnificent training of the Top Basics Course related to the networking genre with full enthusiasm and sincerity.
The high-end institutions of Craw Security at the state-of-the-art premises of Saket and Laxmi Nagar locations offer the Best Networking Course with AI for Beginners that can literally be very beneficial to the understudies looking to initiate a booming career in the networking field.
Furthermore, networking aspirants who sincerely want to learn networking basics from the Top Networking Basics Courses can enroll in our Basic Networking Course with AI in Delhi and learn networking basics with 100% dedication and enthusiasm.
Learners with a decent mood to do something in this trajectory will be given a great opportunity to indulge in this Basic Networking Course with AI in Delhi under the prime leadership of Mr. Mohit Yadav, a renowned cybersecurity expert all over the world.
Book a Trial Demo Class
Training Available 24*7 Call at +91 9513805401

Craw Security High-End Learning Labs






Why join Basic Networking Course from Craw Cyber Security Institute?
An aspiring candidate to learn networking basics can sincerely join the Craw Security campus for the out-of-the-box following USPs:
- Hands-on live practice on the latest devices.
- A practical approach to practice in the latest labs.
- A hands-on experience on the latest networking server racks.
- Dedicated virtual 24Х7 lab access.
Content for In-Depth Basic Networking Course in Delhi
Lesson 01: What is a Network?
Lesson 02: Local Area Network (LAN)
Lesson 03: Wide Area Network (WAN)
Lesson 04: Type of Mode
Lesson 05: Type of Communication
Lesson 01: What is OSI
Lesson 02: Why we Need OSI
Lesson 03: OSI Layers
Lesson 04: TCP/UDP
Lesson 05: 3 Way Hand Shake
Lesson 01: What is TCP/IP
Lesson 02: Why we Need TCP/IP Model
Lesson 03: TCP/IP Layer
Lesson 01: Subnetting Explained
Lesson 02: CIDR (Classless Inter-Domain Routing)
Lesson 03: Create Subnets
Lesson 04: Understanding Variable Length Subnet Masks (VLSM)
Lesson 05: Private IP Addresses Explained
Lesson 01: What is Domain Name System (DNS) and How Does it Work?
Lesson 02: Map Hostnames to IP Addresses
Lesson 03: Configure Cisco Device as DNS client
Lesson 04: How to Configure a Cisco Router as a DNS Server?
Lesson 05: no IP domain-lookup Command
Lesson 06: ARP (Address Resolution Protocol) Explained
Lesson 07: The ARP Table on a Cisco Router
Lesson 01: Network Devices
Lesson 02: Network Hubs Explained
Lesson 03: Network Switch Explained
Lesson 04: CSMA/CD
Lesson 05: Collision & Broadcast Domain
Lesson 06: How Switches Work
Lesson 07: Layer 2 Switching
Lesson 08: Network Router Explained
Lesson 09: What Is Layer 3 Switch and How it Works in Our Network?
Lesson 01: ICMP (Internet Control Message Protocol)
Lesson 02: Ping Explained
Lesson 03: Extended Ping Command
Lesson 04: Traceroute Explained
Lesson 05: Traceroute Command
Lesson 06: show processes Command
Lesson 01: What is APIPA
Lesson 02: Why we Need APIPA
Lesson 03: APIPA (Automatic Private IP Addressing)
Lesson 01: What is ARP
Lesson 02: Why we Need ARP
Lesson 03: Type of ARP
Lesson 01: Routing Protocols
Lesson 02: Comparing Internal Routing Protocols (IGPs)
Lesson 03: Administrative Distance & Metric
Lesson 04: Equal Cost Multi-Path (ECMP) Explanation & Configuration
Lesson 05: Understanding Loopback Interfaces and Loopback Addresses
Lesson 06: passive-interface Command
Lesson 01: What is IP Routing?
Lesson 02: Local Routes and How they Appear in the Routing Table
Lesson 03: Connected, Static, & Dynamic Routes
Lesson 04: Floating Static Route – Explanation and Configuration
Lesson 05: Default Static Route
Lesson 06: Create a Static Host Route
Lesson 01: OSPF Overview
Lesson 02: Differences Between OSPF and EIGRP
Lesson 03: Cisco Bandwidth Command vs Clock Rate and Speed Commands
Lesson 04: OSPF Cost – OSPF Routing Protocol Metric Explained
Lesson 05: OSPF Configuration
Lesson 06: Designated & Backup Designated Router
Lesson 01: Wide Area Network
Lesson 02: Cisco VPN – What is VPN (Virtual Private Network)?
Lesson 03: WAN Connection Types – Explanation and Examples
Lesson 04: Leased Line Definition, Explanation, and Example
Lesson 05: Multiprotocol Label Switching (MPLS) Explained & Configured
Lesson 01: Static NAT
Lesson 02: Dynamic NAT
Lesson 03: Port Address Translation (PAT) Configuration
Lesson 01: What are ACLs
Lesson 02: Types of ACLs
Lesson 03: Configuring Standard ACLs
Lesson 04: Configuring Extended ACLs
Lesson 05: Configuring Named ACLs
Lesson 01: DHCP & DNS
Lesson 02: Configure Cisco Router as DHCP Server
Lesson 03: DHCP Relay Agent
Lesson 04: Configure Cisco Router as a DHCP Client
Lesson 05: APIPA (Automatic Private IP Addressing)
Lesson 01: What is Telnet & SSH
Lesson 02: Why we Need Telnet & SSH
Lesson 03: Telnet & SSH
Lesson 04: Setting Up Telnet
Lesson 05: Setting Up SSH
Lesson 01: What is Network Redundancy and What are its Benefits
Lesson 02: Cisco First Hop Redundancy Protocol (FHRP) Explained
Lesson 03: Cisco Hot Standby Router Protocol (HSRP) Explained
Lesson 04: Cisco Hot Standby Router Protocol (HSRP) Configuration
Lesson 05: Cisco Hot Standby Router Protocol (HSRP) Preempt Command
Lesson 01: What is Layer
Lesson 02: Why we Need Layer 2 Protocol
Lesson 03: CDP
Lesson 04: LLDP
Lesson 01: What is a VLAN?
Lesson 02: Configuring Access & Trunk Ports
Lesson 03: Configuring Voice VLANs
Lesson 04: Configuring Allowed VLANs
Lesson 05: Cisco Dynamic Trunking Protocol (DTP) Explained
Lesson 06: What is VTP
Lesson 07: VTP Modes
Lesson 08: VTP Configuration
Lesson 01: Network Bridge Explained
Lesson 02: How STP Works
Lesson 03: Electing the Root Switch in STP
Lesson 04: Spanning Tree Priority: Root Primary and Root Secondary
Lesson 05: Selecting STP Root Port
Lesson 06: Selecting STP Designated Port (DP)
Lesson 01: What is Ether Channel and Why Do We Need It?
Lesson 02: Ether Channel Port Aggregation Protocol (PAgP)
Lesson 03: Ether Channel Link Aggregation Control Protocol (LACP)
Lesson 04: Multi chassis Ether Channel (MEC) and MEC Options
Lesson 05: Cisco Layer 3 Ether Channel – Explanation and Configuration
Lesson 01: Cisco Console Port Security
Lesson 02: Exec-timeout Command
Lesson 03: Encrypt Local Usernames and Passwords
Basic Networking Course with AI Modules:
Basics of Networking:-
• What is networking?
• Types of networks (LAN, WAN, MAN, etc.)
• Introduction to the OSI and TCP/IP models
• Key networking devices (routers, switches, firewalls)
Role of AI in Networking:-
• Use cases of AI in network optimization
• AI-driven network monitoring and troubleshooting
CCNA Core Concepts:-
• IP addressing and subnetting
• VLANs and trunking
• Routing and switching basics
AI-Assisted Learning Tools:-
• Subnet calculators with AI guidance
• Interactive routing simulators
Static and Dynamic Routing:-
• Static routing configuration
• Dynamic protocols: RIP, EIGRP, OSPF (introduction and
configuration)
• Advanced OSPF configurations (multi-area)
Switching Concepts:-
• MAC address tables
• STP and EtherChannel
• Inter-VLAN routing
AI for Optimization:-
• AI-based route optimization
• Automated troubleshooting for routing loops or misconfigurations
Access Control Lists (ACLs):-
• Standard vs. extended ACLs
• Configuration and testing ACLs
Network Security:-
• Firewall basics
• Securing routers and switches
AI in Security:-
• AI-based intrusion detection systems
• Network behavior analysis
DHCP and DNS:-
• Configuration and troubleshooting
• Integration into larger networks
NAT (Network Address Translation):-
• Static, dynamic, and PAT
AI and Automation:-
• Basics of network automation with Python
• AI-driven configuration management
EIGRP:-
• Concepts and configuration
• EIGRP vs. OSPF (pros and cons)
Redistribution:-
• OSPF and EIGRP route redistribution
• Filtering routes using ACLs
Troubleshooting Tools:-
• Ping, Traceroute, Telnet, SSH
• Packet analysis with Wireshark
AI for Troubleshooting:-
• Predictive analytics for network health
• Automated fault detection and resolution
• Simulated network scenarios with AI guidance
• Configuring OSPF, EIGRP, and ACLs with real-time feedback
• AI tools to optimize lab performance
Designing and deploying a network with:-
• VLANs, OSPF/EIGRP routing
• ACLs for security
• AI monitoring tools
• Real-world scenarios and troubleshooting
• Preparing for the CCNA certification exam
• Career paths in AI-driven networking
Networking Course Online
With a prime commitment towards providing all The Fundamentals of Networking with AI via a genuine Basic Networking Course with AI to learn networking basic concepts to thrive better in the networking background, the institutions of Craw Security at Saket and Laxmi Nagar locations engage its best trainers as faculties to impart quality training on a VILT (Virtual Instructor-Led Training) Networking Course Online to networking aspirants to learn networking basic at their pace with rich course content in the dedicated curriculum.
Basic Networking Course Highlights
- Fundamentals of Networking and Defence Techniques
- Implementing Network Security Controls and Protocols
- Designing and Implementing Network Security Policies
- VPN Security
- Configuring Host Security, File System Encryption and Firewall Implementation
- Network Security Threats and Vulnerabilities
- Monitoring and Analysing Network Traffic
- Network Risks and Vulnerabilities and Network Incident Response
Who should join the Basic Networking Course?
- Anyone who wishes to learn networking basic from the most experienced trainer and mentors.
- If you want to start your networking journey from any other IT field.
- In case you want to learn networking from the scratch.
Choose Your Preferred Learning Mode

Classroom Training
We offer customized VILT (Virtual Instructor-Led Training) sessions at your convenient hours to provide effortless training.

Online Training Class

Corporate Training
Hire a preferred trainer at your work premises at your chosen time slots and train your employees with full efficiency.
Basic Networking Course Description
Initially, Craw Security delivers the most comprehensive Basic Networking Course with AI Syllabus that possesses all of The Fundamentals of Networking as the prime course content in the curriculum associated with the Basic Networking Course with AI to learn networking basics with full dedication.
Moreover, a networking aspiring candidate can essentially demonstrate all the networking skills that one would learn networking basics via the primetime Basic Networking Course with AI duly offered by Craw Cyber Security Institution via its two main branches in Delhi at Saket and Laxmi Nagar locations.
There are almost 4 Types of Networking categories are there as follows:
- LAN (Local Area Network)
- PAN (Personal Area Network)
- MAN (Metropolitan Area Network)
- WAN (Wide Area Network)
Craw Security's Students Awarded










Networking Course with Certification
When it comes to learning networking basic skills from the Best Networking Course with AI for Beginners, Craw Security’s name comes at the leading tech frontiers to deliver its remarkable presence for Basic Networking Course with AI for everyone who sincerely wants to learn networking basic.
In addition, we deliver our excellence in providing a worthwhile Networking Course with Certification which is duly valid in almost all IT organizations as a remarkable and credible source to gather authentic networking knowledge. Moreover, learners who complete their respective Basic Networking Courses will certainly be awarded a proper certificate that will definitely help them showcase the skills they learned during training sessions of the Basic Networking Course at Craw Security.
Related Cyber Security Course
Latest Blogs
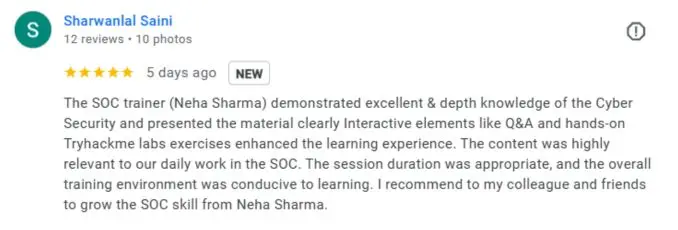
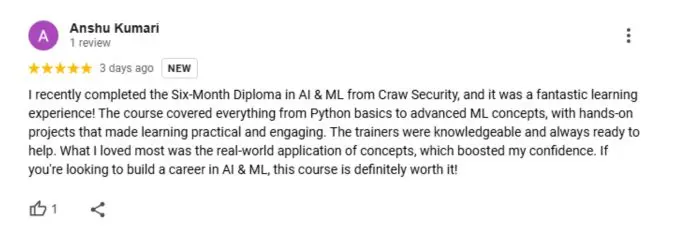
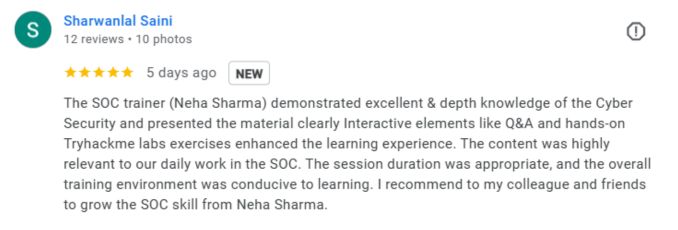
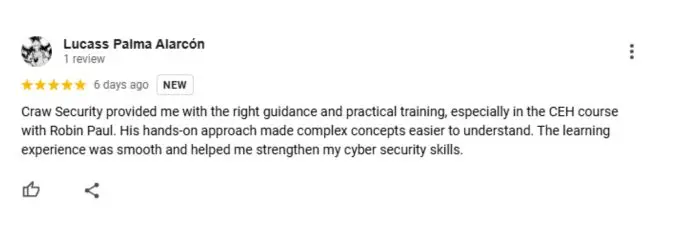
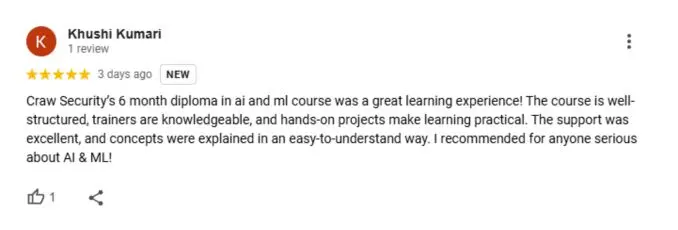
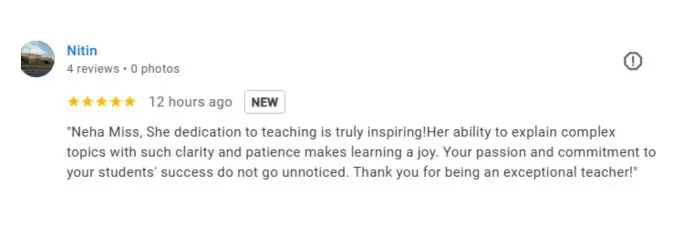
What People Are Saying About Craw Security
Google Review (2000+) ★★★★★
Companies you can get placements in

Basic Networking Frequently Asked Questions
All the fundamentals of networking associated with the Basic Networking Course with AI in Delhi describe the prime factors of networking essentials. One can sincerely conduct the Basic Networking Course with AI in Delhi interactive live classroom sessions from the most experienced and skilled teaching faculties possessing 10+ years of experience in fundamental training associated with the Basic Networking Course through Craw Cyber Security Institute.
The top best networking courses with AI in Delhi are mentioned below:
- Basic Networking Course with AI in Delhi from Craw Security
- Cisco DevNet Associate.
- Cisco CCIE Security.
- Cisco CCIE Enterprise Infrastructure.
- Checkpoint CCSA.
- Checkpoint CCSE.
- Palo Alto Networks (PCNSE)
- Certified Penetration Testing Professional (CPENT)
- AWS Solutions Architect Associate.
You can certainly start a decent career in the Networking genre by the following means:
- You may select Computer Networking as a specialization in the Post-Graduate or PG Diploma Course after successful completion of your graduation in the preferred streamline.
- You can also do some vendor-provided courses like Basic Networking Course with AI in Delhi from Craw Security, CCNA Certification from CISCO, etc.
The main four Types of Networking specializations are as follows:
• LAN (Local Area Network)
• PAN (Personal Area Network)
• MAN (Metropolitan Area Network)
• WAN (Wide Area Network)
You may easily start your study sessions of networking class via the following institutes:
- Basic Networking Course with AI in Delhi from Craw Security.
- CCNA Certifications from Cisco.
- Network Bulls
- Simplilearn
- Udemy
Since there is a vast demand for Networking Associates, Networking Executives, and Networking Engineers, in IT organizations, an aspirant can forecast oneself what is the future of networking.
Yes, learning networking fundamentals is a good choice as the genre of networking is sincerely in demand, as per the study conducted by an independent organization IT Career Finder, the network administrator’s job has taken a dedicated spot in the Top 10 positions.
Yes, it is globally recognized that networking professionals have left a massive impact on the IT industry. India, on the other hand, is not away from this impact as our country is one of the fastest-growing IT industries in the world. Thus, joining a networking league is certainly a good career choice in India for the coming future.
Dedicated coding skills are highly required and recommended for networking, but it also depends on the knowledge of the network engineer, who possesses the necessary information about the coding languages.
A qualified network engineer always possesses a decent knowledge associated with programming languages such as Python, Java, C++, etc.
The thing totally depends upon the learning capabilities of a candidate who is learning the basic fundamentals associated with the Basic Networking Course with AI in Delhi.
However, we can say that Networking falls under the mid-category of hard courses as it falls behind the Science and Engineering streamlines while coming far tougher than the courses associated with the Arts and Humanities streams.
A collection of several computer systems that are connected to one another is what we mean when we talk about a computer network. The connection to a network can either be wired (by means of cable) or wireless. Using both hardware (cables, routers, switches, access points, and so on) and software (operating systems or business applications), we are able to set up a computer network.
Yes, you may learn networking on your own with the help of multiple YouTube channels and other prominent modes. However, these channels will only give you knowledge about a particular topic but cannot guide you to your errors distinctively. For this, you need to join a particular training program offered by an accredited and recognized training institute, like Craw Security.
A computer network is a set of rules that determines how a computer can communicate with another computer that is located at a distance. In the event that you are a computer nerd who enjoys finding solutions to problems and has a fundamental understanding of programming, mastering networking should not be difficult for you.
The duration of the basic networking course with AI differs from institute to institute. However, at Craw Security, you will find this exciting course with a duration of 60 hours only.
The mainstream topics covered in this basic networking course with AI are as follows:
- Module 1: Introduction to Networking and AI Integration
- Basics of Networking
- Role of AI in Networking
- Module 2: Network Fundamentals
- CCNA Core Concepts
- AI-Assisted Learning Tools
- Module 3: Routing and Switching
- Static and Dynamic Routing
- Switching Concepts
- AI for Optimization
- Module 4: Access Control and Security
- Access Control Lists (ACLs)
- Network Security
- AI in Security
- Module 5: IP Services and Automation
- DHCP and DNS
- NAT (Network Address Translation)
- AI and Automation
- Module 6: Advanced Routing Concepts
- EIGRP
- Redistribution
- Module 7: Network Monitoring and Troubleshooting
- Troubleshooting Tools
- AI for Troubleshooting
- Module 8: AI-Enhanced Lab Sessions
- Module 9: Final Project
- Module 10: Certification and Career Path
The premium Basic Networking Course with AI by Craw Security is a highly practical-based course taken under the prime guidance of world-class training instructors with a proven track record of offering hands-on training to all learners in both offline and online training methodologies. For more info, call at +91-9513805401.
Yes, you will get a certificate from FutureSkills Prime, a MeitY –NASSCOM, Digital Skilling Initiative, after passing an online exam on their portal, which is highly valid throughout the world for its ultimate value due to the GOI-approved course.
No, there are no specialized prerequisites needed to enroll in this course. A person with a non-IT background can also seek admission to this course.
Yes, this course is duly available in both online as well as offline modes.
We also deliver the best price for the cost of each course at Craw Security. You just need to call us on our hotline mobile number, +91-9513805401, and have a word with our highly qualified and skilled educational consultants for a quick word in this matter. They will guide you better.
Yes, we do offer “100% Job Assistance” for every in-house course at Craw Security. However, if a person completes our 1 Year Diploma in Cyber Security Course, we will deliver them with a “100% Placement Guarantee” for sure.
A collection of several computer systems that are connected to one another is what we mean when we talk about a computer network. The connection to a network can either be wired (by means of cable) or wireless. Using both hardware (cables, routers, switches, access points, and so on) and software (operating systems or business applications), we are able to set up a computer network.
Yes, you may learn networking on your own with the help of multiple YouTube channels and other prominent modes. However, these channels will only give you knowledge about a particular topic but cannot guide you to your errors distinctively. To do this, you need to join a particular training program offered by an accredited and recognized training institute, like Craw Security.
A computer network is a set of rules that determines how a computer can communicate with another computer that is located at a distance. In the event that you are a computer nerd who enjoys finding solutions to problems and has a fundamental understanding of programming, mastering networking should not be difficult for you.








