Certified Ethical Hacker CEH v13 AI Course in Delhi, India
September 10, 2022 2025-04-28 15:13Certified Ethical Hacker CEH v13 AI Course in Delhi, India
CEH v13 Ai Course in Delhi | EC Council Certified Ethical Hacker Course
Learn the very famous EC Council CEH v13 Ai Training and Certification Course in Delhi with the best specializations of ethical hacking fundamentals through the most versatile faculty members imparting quality mentorship on the verified syllabus of Certified Ethical Hacker on the latest 13th version with a massive leniency towards Artificial Intelligence. In addition, learners will get a fully intensified classroom experience on the latest updated technological software of CEH v13 Ai Training and Certification 20 modules.
Moreover, after the successful completion of the Certified Ethical Hacker v13 Ai course, a person will certainly be able to hack into systems from any remote location and secure them like a professional Security Analyst in the coolest way possible via the techniques and tactics that you will learn from our verified curriculum from EC Council in our authentic CEH Training in Delhi through its latest edition of CEH v13 Ai.
- Course Duration : 40 Hours
- Language : Hindi | English
- Course Delivery : Online | offline
Book a Trial Demo Class
Training Available 24*7 Call at 9513805401
What will you learn in CEH v13 Ai Training in Delhi?
Any person who is proactively interested in learning and building an outstanding career in the stream of Cyber Security and Ethical Hacking Course in Delhi can nicely get the enrollment in this highly versatile training of Ethical Hacking Course in Delhi after 12th for starting your career in the domains of Information Security so nicely. In addition, Craw Security is the best cyber security institute in India, with the verified curriculum of EC Council CEH v13 Ai Syllabus directly from the house of EC Council.
Now, it is pretty high time for a person who wants to shine as a cyber security professional to seek admission to the CEH v13 Ai Course in Delhi which would certainly assist you in mastering the fundamental skills of ethical hacking. Moreover, to master the CEH Certified Ethical Hacker concepts, one needs to understand the basic concepts through our well-qualified and duly experienced training instructors having more than 10 years of quality industry experience.
Craw Security's High-End CEH v13 AI Labs






Worldwide Release of Certified Ethical Hacker v13 Ai
As per the C|EH Threat Report, malevolent actors are using AI more frequently to carry out unprecedented cyberattacks. In this regard, security experts should now know the methodologies to counter AI-based tactics to repel these attempts.
Moreover, the following basic factors were discovered by the EC-Council during a recent worldwide assessment of ethical hackers in C|EH Threat Report:
- According to 95% of security leaders, neutralizing AI risks requires AI expertise.
- 83% of ethical hackers reported that during the AI revolution, their attack techniques saw noticeable changes.
- The majority of ethical hackers — 66% — admitted that they were unprepared for the AI cyberattacks.
Hence, Craw Security is now providing you the best session in a bonus chapter featuring Artificial Intelligence or AI as the prime resource to catch in today’s world along with the knowledge imparted by our trainers in CEH v13 Ai Certification Training.
Book a Trial Demo Class
Training Available 24*7 Call at +91 9513805401

Content for CEH v13 Ai Course in Delhi
Module 01: Introduction to Ethical Hacking
Module 02: Footprinting and Reconnaissance
Module 03: Scanning Networks
Module 04: Enumeration
Module 05: Vulnerability Analysis
Module 06: System Hacking
Module 07: Malware Threats
Module 08: Sniffing
Module 09: Social Engineering
Module 10: Denial-of-Service
Module 11: Session Hijacking
Module 12: Evading IDS, Firewalls & Honeypots
Module 13: Hacking Web Servers
Module 14: Hacking Web Applications
Module 15: SQL Injection
Module 16: Hacking Wireless Networks
Module 17: Hacking Mobile Platforms
Module 18: IoT Hacking
Module 19: Cloud Computing
Module 20: Cryptography
Talk to Our Course Advisor
What will you learn in Certified Ethical Hacker v13 Ai Training in Delhi?
Craw Security will certainly define all the essential concepts and useful details that a person requires to choose this mesmerizing CEH v13 Ai Training in Certification Course in Delhi from the House of EC-Council. In this upcoming 13th edition of Certified Ethical Hacker, people will learn the power of Artificial Intelligence in this booming industry of information security along with other prominent factors like Machine Learning, WormGPT, ChatGPT, etc. Furthermore, Craw Security – the best cyber security training institute in Delhi NCR is offering the best-in-class CEH v13 Ai Training and Certification Course under the mentorship of proactive trainers and mentors having 12+ years of quality experience.
Enroll today in the Certified Ethical Hacker Course with us and become a specialized person in ethical hacking with the unconditional support of Craw Security – the primetime official learning partner of EC Council to impart its valuable knowledge-based courses at its premises in the Saket and Laxmi Nagar branches. We provide the Best EC-Council Certified Ethical Hacker CEH v13 Ai Training and Certification in Delhi.
The CEH Certified Ethical Hacker v13 Ai (CEH v13 Ai Course in Delhi) program is a very popular information security training program among information security professionals. Enrolling in a CEH v13 Ai Course in Delhi helps in covering all concepts in the objectives so that you can master the knowledge needed to clear the CEH Exam.
Choose Your Preferred Learning Mode

Classroom Training
We offer customized VILT (Virtual Instructor-Led Training) sessions at your convenient hours to provide effortless training.

Online Training Class
One can also opt for the prerecorded video sessions available at any point of time from any particular location.

Corporate Training
Hire a preferred trainer at your work premises at your chosen time slots and train your employees with full efficiency.
EC-Council CEH v13 Ai Course Description
Future Proof Your Cybersecurity Career with AI
The Demand for Cybersecurity Professionals with AI Skills is on the Rise. AI Skills are no longer ‘Optional’; They are utmost ‘Essential.’
- AI is actively used by 42% of large businesses, and 59% of early adopters intend to boost spending and quicken AI integration. (IBM, 2025).
- 40% increase in demand for machine learning and artificial intelligence experts. (World Economic Forum, 2025).
- Because AI solutions are fast and effective, 96% of security leaders believe they are necessary for countering AI-powered threats. (Darktrace, 2025).
- According to 87% of corporate leaders, at least 25% of their workforce will require artificial intelligence upskilling. (IBM, 2025).
AI in Cybersecurity
Threats
- 83% note tangible alterations in attack methodologies amidst the AI revolution (EC-Council, 2025).
- 66% admit Being Unprepared for AI Cyber Onslaughts (EC-Council, 2025).
Countermeasures
- AI models have the potential to reduce fraud costs by up to 90% in some cases where behavioral data analysis is used effectively (IBM, 2025).
- Businesses saved USD 850,000 and shortened breach lifecycles by 108 days because of AI and automation, which reduced breach effect by 30% (IBM, 2025).
In addition to offering a wealth of practical guidance, the CEH v13 incorporates AI into each of the five stages of ethical hacking:
Learn AI to automate tasks related to ethical hacking, safeguard against AI systems, and increase task productivity by 40% in your professional capacity.
Acquire a Hacker Mentality: Learn how to automate the five phases of ethical hacking with AI skills.
- Reconnaissance: Learn to gather essential information about your target
- Vulnerability Scanning: Gain the ability to identify weaknesses in the target system
- Gaining Access: Learn how to actively exploit identified vulnerabilities
- Maintaining Access: Develop skills to maintain continued access to the target systems
- Clearing Tracks: Master the art of erasing any trace of your activities
CEH v13 AI | Learn AI Tools in version 13 of CEH:
- ShellGPT,
- ChatGPT,
- FraudGPT,
- WormGPT,
- DeepExploit,
- Nebula,
- io, and many more!
In case you are desperately searching for an institution that is duly accredited and affiliated with the EC Council then your search is over as Craw Security is one of the prominent cyber security institutions in Delhi that is duly accredited to the EC Council as an authorized learning partner to provide its courses. Craw Security is duly present at Saket and Laxmi Nagar locations in Delhi NCR for a decade-long run imparting a quality-based education system in information security for professional Ethical Hacking Course in Delhi.
By delivering the crucial Eccouncil CEH v13 Ai Course in Delhi, we have become one of the Top 10 Ethical Hacking Institutes in Delhi. While learning here, you will get proper Training & Certifications in the Ethical Hacking Course so that you can also use techniques and tactics duly utilized in the industry by the Best Ethical Hackers and Penetration Testing Experts from this field.
The main benefits of taking a CEH v13 Ai Course in Delhi are:
- It provides the breadth of coverage necessary to learn the full security concepts behind the CEH exam.
- It assists prepare you for a career as a Cyber security professional.
- If you want to make a career in Cyber Security then getting admission to the ethical hacking v13 Ai training and certification program is quite essential. CEH v13 Ai Course in Delhi is a leading training and certification program where Students audit a system for weaknesses and vulnerabilities using the same tools and exploits as malicious hackers, but having proper legal rights and working towards the cyber security of an organization. One of the most important things about being a proficient hacker is that you understand the psyche of how a hacker’s brain works.
- By taking the CEH v13 Ai Course in Delhi, you will be in a better state to be at the helm of an organization’s cyber security. In today’s day and age, when cyber security is a top priority in every organization, taking up a Certified Ethical Hacker v13 Ai Course will give you an edge over others in this field. The Certified Ethical Hacker (CEH v13 Ai) program is the most coveted information security training program any information security professional wants to learn. Completing this course help you in acquiring hacking technologies within the legal framework of the country, which you can use in ethical ways. Getting training in this course gives you proper knowledge of advanced hacking tools and techniques used by hackers and information security professionals across the globe.
- Workshops & Seminars: We Provide Workshops and Seminars to Fill the Gap Between Industry requirements and Students’ Skills.
- 100% Job Guaranteed: At Starting Package 4-5 Lacs per annum After EC-Council Training from Craw Cyber Security Institute.
There is a vast scope of Certified Ethical Hacker Jobs in the world whereas India spots no less than anyone else in the world rankings providing most of the crucial Certified Ethical Hacker Salary in India associated with the varied domains of Cyber Security.
Our alumni network is functioning distinguishedly at various levels in reputed organizations after undergoing the Best Certified Ethical Hacking Course in Delhi from Craw Cyber Security Institutions at Saket and Lakshmi Nagar locations.
People are widely seen searching for the Certified Ethical Hacking Course in Delhi Fees as well as the Certified Ethical Hacker Exam Cost to know more about the financial aspects for our budget students. They are equally worried about how to get CEH Certification from any verified institution in their locale.
The domain aspirants are also seen searching for the Certified Ethical Hacker Salary in varied organizations to know the lifestyle they will get after pursuing a suitable career in the domain from the thorough learning of CEH v13 Ai Training in Delhi with the exciting and highly booming technology of Artificial Intelligence and machine learning from an accredited institute from reputed ECcouncil just like Craw Cyber Security Institution.
We have developed a series of a questionnaire and their answers so that may get an understanding of the most frequently asked questions on this particular topic of Certified Ethical Hacker Training:
Craw Security's Students Awarded










Key Features of Certified Ethical Hacker Course in Delhi:
- Introduction to Basics of Ethical Hacking
- In-depth Network Scanning
- System Hacking Password Cracking & Bypassing
- Mobile Hacking
- Web Session Hijacking
- Viruses and Worms, Trojan and Back Door, SQL Injection Manual Testing
- Hacking Webservers Server Rooting, Hacking Wireless Network, Penetration Testing: Basics
- Internet of Things (IoT) Hacking, Cloud Security, and many more.
Related Cyber Security Course
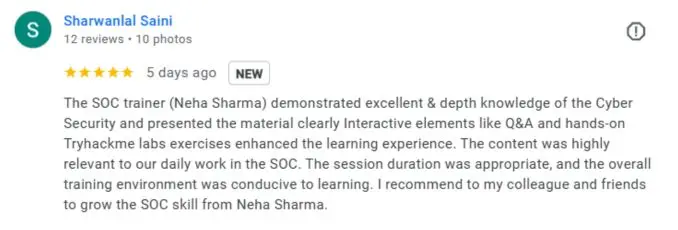
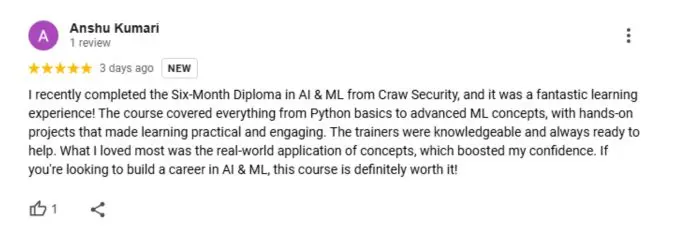
What People Are Saying About Craw Security
Google Review (2000+) ★★★★★
Frequently Asked Questions
About CEH v13 Ai Course in Delhi and Certification Institute
The most recent ethical hacking methods, tools, and tactics are the topic of the internationally recognized Certified Ethical Hacker (CEH) v13 certification. To address cybersecurity challenges and solutions powered by artificial intelligence (AI), it has a dedicated section on AI.
By completing CEH v13, you will gain knowledge in:
- Identifying and addressing security weaknesses
- Utilizing hacking tools and techniques
- Securing systems and networks against attacks
- Implementing AI tools to detect and counter advanced threats
- Handling AI-driven cyber-attacks
AI is being utilized more and more in cybersecurity operations, both offensive and defensive. The AI module gives ethical hackers the know-how to recognize and neutralize threats based on artificial intelligence (AI) and to use AI technologies to strengthen cybersecurity defenses.
Prerequisites are not required in order to take CEH v13. However, it is advised to have a solid grasp of system administration, networking, and cybersecurity. It can also be beneficial to have prior experience with penetration testing or ethical hacking.
It typically takes five to six days, depending on the learning format, to complete the CEH v13 course. This covers both didactic instruction and interactive laboratory exercises. Additionally, some institutions have self-paced choices that could take longer to complete.
The CEH v13 certification makes positions like:
- Ethical Hacker
- Penetration Tester
- Cybersecurity Analyst
- Security Consultant
- Security Administrator
- AI Security Specialist
Yes, CEH v13 is regarded as a premier certification in ethical hacking and cybersecurity by numerous government agencies, businesses, and academic institutions throughout the world.
With 4 hours to spare, candidates must answer 125 multiple-choice questions on the CEH v13 exam. Exam topics include network security, information security, and artificial intelligence in cybersecurity.
Depending on the location and training provider, the cost of the CEH v13 with AI certification might vary, but it normally falls between $1,200 and $2,000 and includes hands-on laboratories, training materials, and exam fees.
Getting ready for the CEH v13 test entails:
- Attending formal training from an accredited provider
- Practicing real-world hacking tools and labs
- Studying AI-based cybersecurity technologies
- Reviewing official CEH study guides and practice exams
Yes, the cybersecurity industry places great importance on CEH v13. It attests to your proficiency in AI-driven security and ethical hacking, which can greatly improve your chances of landing a job in any number of security-related fields.
The material of CEH v13 has been updated to reflect the most recent cybersecurity risks and remedies. One of the most significant additions to v13 is the AI module, which focuses on using artificial intelligence to both attack and defend IT infrastructure.
Every few years, the EC-Council updates the CEH curriculum to reflect the latest advancements in cybersecurity best practices, technology, and threats. The most recent version, CEH v13, includes state-of-the-art methods and instruments.
Yes, although having past hacking expertise might be helpful, the CEH course is also meant for those who are new to the field. The course provides both practical experiments to enhance your abilities from the bottom up and foundational knowledge.
The CEH v13 certification is widely accepted as a prerequisite for cybersecurity positions in a number of industries, including IT, finance, government, healthcare, and consulting.
You may learn Ethical Hacking in Delhi with the EC Council CEH v13 Ai Training and Certification Course under the mentorship of primetime trainers and mentors having more than 10 years of quality experience by Craw Security – the best cyber security training institute in Delhi NCR at Saket and Laxmi Nagar branches.
From the valuable accreditation of EC Council – a giant in the industry of spreading quality education in Cyber Security Courses, doing a course like Certified Ethical Hacker is certainly worthwhile.
However, there are varied ethical hacking courses duly available in the wild from many cyber security training institutions in the market but we will suggest you learn your maiden ethical hacking fundamental concepts from the EC Council CEH v13 Ai Course in Delhi by Craw Cyber Security Institute at Saket and Laxmi Nagar branches.
Nothing is difficult for a person who has an eagerness to learn things thoroughly. Hence, we suggest you learn the things precisely while learning in your respective classroom or online sessions of the CEH v13 Ai Training and Certification Course so that you can never miss any crucial concept that may put a burden on your shoulders while sitting in the CEH v13 Ai Exam.
There are many institutes in the market that tend to be the best ones for ethical hacking training in their respective vicinity, however, we will suggest you thoroughly check the number of affiliations and accreditations before enrolling for any course in the particular institute. In the same context, Craw Security has a number of affiliations and accreditations that will certainly make this institute the best ethical hacking training institute in Delhi NCR remarkably present at Saket and Laxmi Nagar branches.
You can easily do a Certified Ethical Hacker Course in Delhi from Craw Cyber Security Institute located in two prime locations of Saket and Lakshmi Nagar in New Delhi, India for only ₹35,000/- + Taxes.
Yes, from our premium and dedicated institute of Craw Cyber Security Institution in Saket and Lakshmi Nagar in New Delhi, India, anyone with a minimum of 10th passed certificate from any recognized board in India can join and get oneself CEH v13 Ai Certified from the wonderful curriculum duly recognized by EC Council.
Yes, it’s very certain that pursuing the Certified Ethical Hacking Course in Delhi is a good and shinier career ahead in case you have a keen interest in Ethical Hacking and a Cyber Security background. One can nicely join our Certified Ethical Hacking Training and Certifications from Craw Cyber Security Institute in Saket and Laxmi Nagar locations and learn from scratch to become a genuine Cyber Security professional in the shortest possible time.
As per PayScale – an independent Salary accounting organization, the median base pay of EC Council CEH v13 Ai Certification holder ethical hacking professional is something around ₹5,13,333/- annually.
The main functions done by an EC-Council Certified Ethical Hacker are to find the loopholes in the form of threats and vulnerabilities in the servers of a particular website, network, or the IT infrastructure of an organization and secure them by finding the perfect strategy and in the shortest time possible.
There are many programming languages in the world widely used by numerous types of potential hackers like Python, Java, C, C++, etc. But most hackers use Python as their main coding language partner to do their various hacking stuff in the world. So researchers of the domain also say that Python Programming Language has also been immensely used by many Black Hat Hackers around the world.
Most of the famous Cyber Security and Ethical Hacking Courses in Delhi NCR want a Bachelor’s degree (BSc, BTech, BE, BCA) in Information Technology or Computer Science to become an ethical hacker whereas Craw Cyber Security is one of the few institutes that provides its genuine curriculum of CEH v13 Ai Certified Ethical Hacking Course in Delhi with a minimum 10th passed certificate from any recognized board in India.
- Computer Networking Skills.
- Computer Skills
- Linux Skills
- Basic Hardware knowledge
- Cryptography Skills
- Database Skills
There is no particular job in this world for potential Black Hat Hackers as it is an illegal activity to perform and it is also banned by various governments in the world but having genuine knowledge of the Ethical Hacking and Cyber Security field will definitely land in some decent positions in some reputed organizations in the world.
Companies you can get placements in









